UK Government leaked its budget because of a WordPress plugin


On November 26, 2025, the Office for Budget Responsibility (OBR) accidentally released its Economic and Fiscal Outlook nearly an hour before Chancellor Rachel Reeves delivered the Autumn Statement. Within minutes, Reuters and other news outlets reported figures from the report, including tax measures projected to raise £26.1 billion. This premature disclosure disrupted the Chancellor’s speech and undermined the OBR’s credibility. Its oversight board later labeled the incident the worst failure in the organization’s 15-year history. All over a WordPress plugin!
Basically, a routine content management workflow, a misused plugin, and inadequate server protections led to eager reporters accessing the information. You think this can’t happen to you? Think again!
Why the OBR used WordPress
The OBR hosts its website on WordPress through WP Engine. Publishing the autumn and spring forecasts involves significant logistical coordination, requiring dozens of PDFs and spreadsheets to be ready as soon as the Chancellor begins their speech. T
o prevent delays, staff and an external web developer preload files into WordPress a few hours before the embargo lifts, believing that WordPress’s private status would keep these drafts hidden while relying on the hosting provider’s security to prevent unauthorized access. Unfortunately, this assumption was… a bit misguided.
Timeline of the leak
Probing and upload
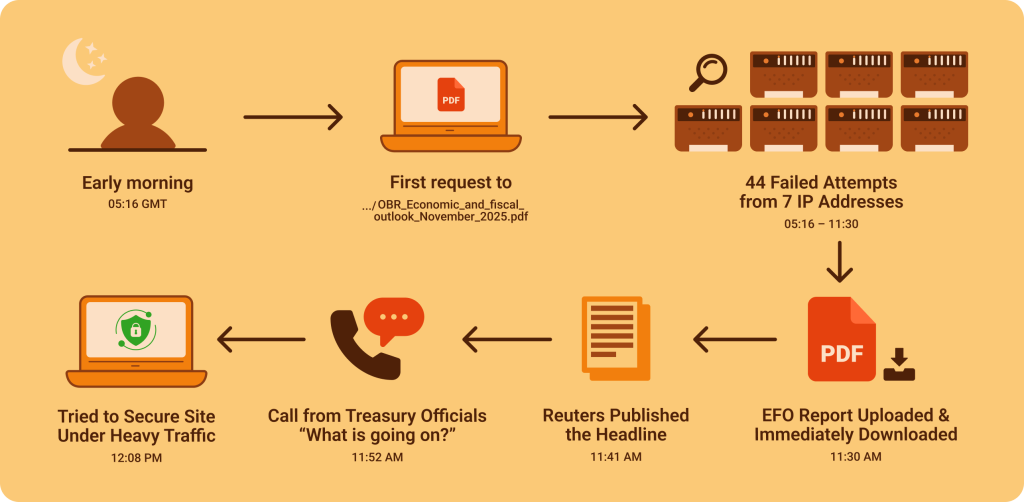
Log files indicate that someone began probing the OBR site early in the morning. At 05:16 GMT, the first request hit the path .../OBR_Economic_and_Fiscal_Outcome_November_2025.pdf. Between then and 11:30, there were 44 unsuccessful attempts from seven distinct IP addresses, suggesting that the observers were guessing the month in the URL based on previous reports.
At 11:30, the web developer uploaded the EFO PDF. Seconds later, the same IP address that had been probing successfully downloaded the file. In the next 32 minutes, 43 unique IP addresses accessed the report. At 11:41, Reuters published a headline citing figures from the document. The OBR team became aware of the issue only after being alerted by Treasury officials at 11:52. They attempted to remove the PDF and password-protect the site, but heavy traffic hampered their efforts; the file remained accessible until 12:08.
Aftermath
The incident affected markets and embarrassed the new government. The oversight board acknowledged that the leak inflicted significant reputational damage. It recommended a forensic audit of previous releases after uncovering indications that a similar early access occurred in March 2025. The board also urged the OBR to transition its web-publishing process to a central government domain with enhanced safeguards.
The technical root cause
Predictable URLs and a misused WordPress plugin
The OBR used a popular plugin called Download Monitor to manage file downloads. This plugin creates direct URLs to each file in the dlm_uploads directory, making it easy to track downloads. However, without proper setup, it bypasses WordPress’s draft status. The investigation found that the plugin’s ability to create easy-to-access URLs was a known feature. When the developer uploaded the EFO, the plugin generated a path that matched patterns from earlier releases.
WordPress also stores uploads in easy-to-guess directories like /wp-content/uploads/2025/11/Budget.pdf. The Altis team pointed out that WordPress doesn’t have a built-in way to keep uploads private; anything can be accessed if someone guesses the path. While Download Monitor uses a different directory, it has the same issue. The OBR didn’t use the plugin’s paid features for controlling access.
The missing server-level protection
On top of WordPress, the server lacked rules to block direct access to upload directories. Download Monitor supports web server rules, like .htaccess, to restrict file access, but these rules were not set up. The Register clearly described the problem: a misunderstanding of the plugin and a lack of server protections allowed anyone to download the PDF. If the server had returned a 403 Forbidden message for requests to dlm_uploads, the leak could have been prevented.
A common cause of data leaks
The OBR’s mistake isn’t unique. Other organizations have faced leaks after uploading sensitive documents to publicly accessible servers. In Federal Trade Commission v. Microsoft in 2023, the company accidentally uploaded unredacted files to a U.S. district court’s website, revealing details about upcoming Xbox consoles and games. The FTC said that Microsoft was fully responsible for this mistake, noting that confidential attachments were only hidden inside a PDF instead of being properly removed.
In another case, Microsoft’s AI research team unintentionally exposed 38 terabytes of private data when they released open-source training models on GitHub. A README file contained an overly permissive Shared Access Signature (SAS) token that gave full control over an Azure Storage account, including the ability to write and delete files. Anyone following the instructions could access secrets, keys, and internal Teams messages. These incidents show that mistakes and easy-to-guess resource identifiers can lead to serious problems, even for large companies.
Lessons from the UK budget leak
The early release of the EFO affected bond markets and undermined the Chancellor’s announcement. This led to reputational damage, public embarrassment, and a potential loss of investor trust. However, the technical issues involved are easy to fix:
Don’t rely on obscurity
Predictable URLs are not a security measure. Attackers can guess filenames or monitor XML sitemaps. Always combine pre-publication uploads with authentication and proper access control.
Audit third-party plugins
You really need to audit every third-party plugin that you install. Understand how plugins manage files and what default permissions they use.
In the OBR case, the team assumed that a draft post would keep the link private without realizing the plugin created a public URL.
Enforce server-level protections
Set up web server rules or a web application firewall to limit access to upload directories. Don’t rely only on CMS settings for security.
Use randomized identifiers
Avoid naming conventions that make future documents easy to guess. Use random file names or keep drafts in separate environments.
Invest in secure infrastructure
Smaller organizations should get professional hosting and dedicated digital operations staff. Training editors and developers on secure publishing practices can help reduce risks.
The accidental early release of the OBR’s Economic and Fiscal Outlook on November 26, 2025, serves as a critical reminder of how easily sensitive information can be leaked. The situation unfolded due to a mix of predictable URLs, a misconfigured WordPress plugin, and insufficient protections at the server level.
Mistakes like these can lead to significant reputational damage and loss of public trust, as seen with the OBR and other organizations like Microsoft. It highlights that relying on obscurity for security is not enough. Proactive measures are essential.
For anyone managing sensitive information, it’s essential to audit third-party plugins, implement strong server protections, and use randomized identifiers for files. Investing in secure infrastructure and training staff on safe publishing practices can significantly reduce risks. Everyone should take these lessons seriously to avoid becoming the next headline and organizations should focus on building secure infrastructures to effectively safeguard their information.
That’s why reliable hosting solutions are so important. By choosing a secure hosting provider, you can significantly reduce your vulnerability to leaks and breaches. And SpaceLama not only offers robust security features but also expert support, ensuring that your hosting environment is as safe as possible. Investing in such secure solutions is a proactive step that can help protect your organization’s reputation and trustworthiness.
SpaceLama offers clear pricing, honest resource limits, daily-tested backups, fast expert support, and regional data centers so your site runs fast and stays online. Choosing a reliable host now prevents expensive recovery work later. Secure your hosting plan now and unlock the advantages that come with being part of the SpaceLama family.